Almost half of UK utilities and production businesses, including manufacturers, identified a cyber breach or attack in the past year, according to the Cyber Security Breaches Survey 2025/2026. At 49%, the sector sits above the all-business average of 43%, with construction and transport or storage also reporting breach or attack levels of 45%.
The utilities and production category is broader than manufacturing alone, covering mining and quarrying, manufacturing, electricity and gas, water, waste, and remediation. Even with that caveat, the figures give the survey a useful industrial reading. Cyber security has been part of OT, manufacturing, and infrastructure risk management for well over a decade, but the pressure on those controls is increasing as attackers move faster, supply chains digitise further, and operational disruption carries heavier commercial consequences.
The Cyber Monitoring Centre’s analysis of the Jaguar Land Rover incident modelled a £1.9bn UK impact across JLR, suppliers, downstream organisations, logistics providers, dealerships, and local businesses. Its assessment showed how a cyber attack against a major manufacturer can spread through production networks, regional economies, and supply chains that rely on tight sequencing rather than generous slack.
Exposure without ownership
The survey shows uneven board ownership across the industrial base. Utilities and production businesses were slightly above the business average for having a board member responsible for cyber security, at 33% compared with 31% overall. Construction stood at 24%, while transport or storage was lower again, at 17%.
Those figures sit awkwardly beside the way industrial operations have been configured for years. Production scheduling, warehouse systems, building management, quality assurance, remote access, energy management, customer portals, and supplier platforms are linked through digital systems that support output every day. A compromised identity, disrupted cloud service, inaccessible backup, or disabled monitoring system can quickly turn into lost production, delayed shipments, strained cash flow, and disrupted customer commitments.
Merlin Gillespie, CTO of Cybanetix, said the policy framework still treats cyber too narrowly. “They’re treating cyber security as though it’s a private sector hygiene problem rather than nationwide public risk,” he said. “CISO’s are exhausted, not because they don’t know what to do technically, but because they’re overwhelmed with risks, compliance, the audit treadmill and signing off supplier questionnaires.”
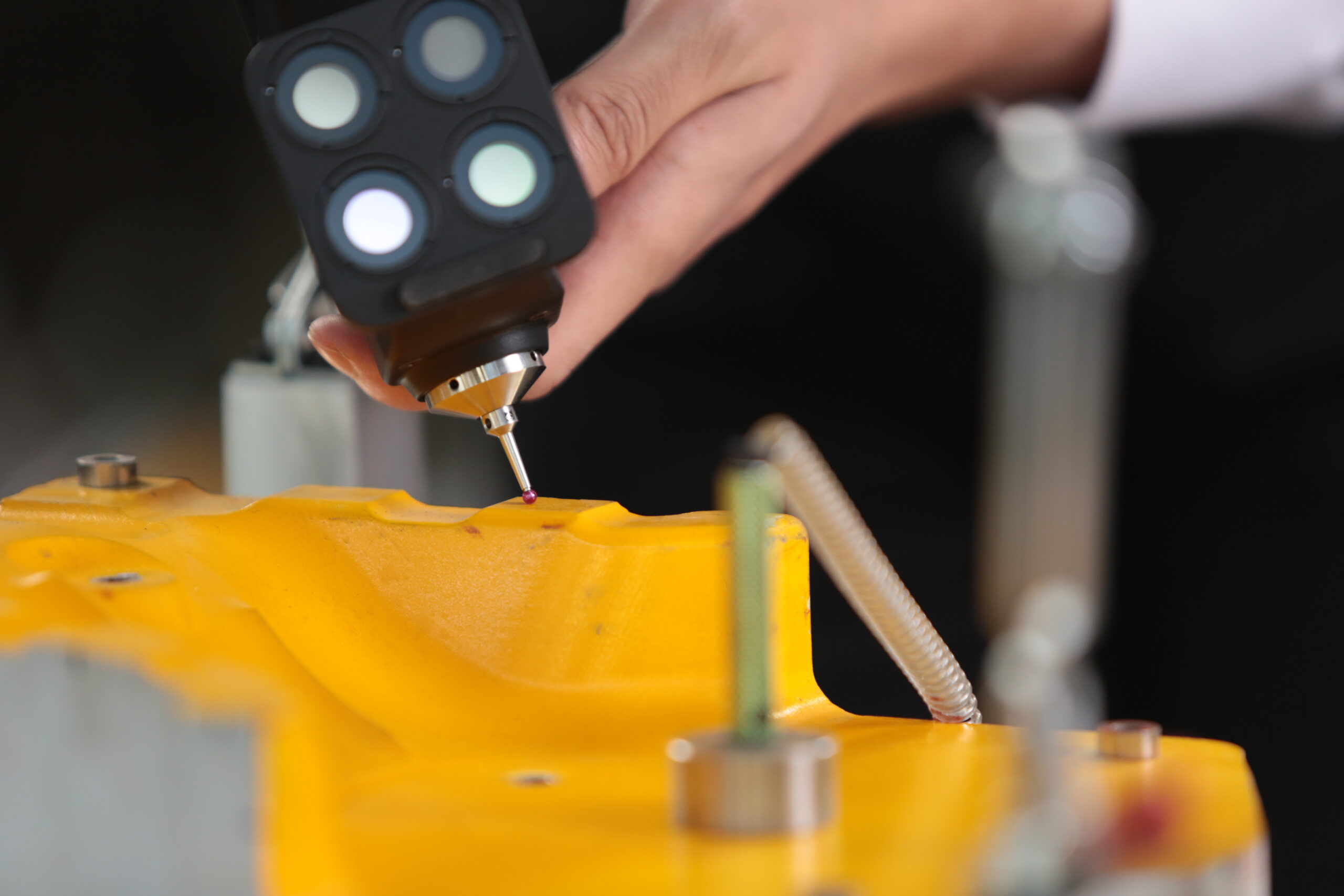
The tension is particularly visible in manufacturing, where cyber controls often collide with legacy plant, long asset lifecycles, and operational technology that was never designed for the current threat environment. One large manufacturing respondent quoted in the survey said: “As a manufacturer, our machines rely on old software and that would not comply with Cyber Essentials.”
That comment captures a practical difficulty for industrial operators. Certification can improve discipline, but it does not erase the installed base of ageing machinery, unsupported software, and production systems that cannot be patched or replaced without operational consequences. Cyber maturity in industrial settings has to account for containment, monitoring, segmentation, compensating controls, and recovery, rather than assuming every asset can be brought neatly into line with modern IT expectations.
Basic controls still expose the wider gap. The survey found that 47% of businesses used two-factor authentication for networks or applications, despite phishing remaining the most common breach or attack type. Michael Downs, VP at SecurEnvoy, said: “Only 47% of businesses have adopted it, meaning a significant proportion of organisations are leaving the door wide open for cybercriminals.”
For industrial companies, MFA is only one control among many, but slow uptake points to a broader implementation problem. If a widely understood measure remains below half of businesses, more complex work around OT visibility, privileged access, supplier connectivity, recovery testing, and identity restoration is unlikely to be consistently embedded across the sector.
Recovery under pressure
The supply-chain figures are among the weakest in the survey. Across all businesses, only 15% reviewed cyber risks posed by immediate suppliers, and just 6% reviewed risks across the wider supply chain. Industrial companies depend on outsourced maintenance, tiered manufacturing, logistics partners, managed IT providers, automation vendors, cloud systems, specialist contractors, and remote support arrangements, all of which create routes for disruption beyond the company perimeter.
Chris Newton Smith, CEO of IO, said the low level of supplier risk review highlighted “a significant systemic vulnerability across organisations.” He added: “While many organisations are investing in strengthening their own internal defences, they are often leaving a critical gap by failing to adequately assess and manage risks within their supply chain — effectively reinforcing the front door while leaving the back door open.”
Regulation is also moving toward tighter accountability. The Cyber Security and Resilience Bill is set to expand the UK’s cyber regime around managed service providers, data centres, large load controllers, and designated critical suppliers. It will introduce a two-stage incident reporting structure, with an initial notification within 24 hours and a fuller report within 72 hours for regulated entities.
Richard Groome, OT Cybersecurity Specialist at e2e-assure, said the new deadlines would require capabilities that many organisations have not yet built. “Meeting those reporting deadlines requires mature SOC processes, 24/7 monitoring, and automated detection capabilities that many smaller organisations simply do not have in place today,” he said.
The survey found that only 25% of businesses overall had a formal incident response plan. In industrial environments, response planning needs to reflect production realities as well as regulatory process. A credible plan establishes which systems are affected, which suppliers and customers may be exposed, what can be safely isolated, which processes can continue manually, and what sequence is required to restart operations without reintroducing risk.
Dan Lattimer, Vice President EMEA at Semperis, said: “Incident response without identity recovery is incomplete response.” Compromised accounts can continue to delay recovery after the initial route of attack has been contained, particularly where production systems, cloud workloads, supplier portals, and remote access tools depend on shared identity infrastructure.
Backups create a similar test. Jon Fielding, Managing Director of EMEA for Apricorn, warned that cyber criminals are “increasingly targeting not the data but the data backups” because doing so prevents recovery and increases leverage. For manufacturers and other industrial operators, the useful measure is not the existence of a backup, but whether it is isolated, immutable, encrypted, tested, and recoverable within the operational tolerance of the business.
The Cyber Security Breaches Survey gives industrial leaders a familiar set of problems with sharper consequences. Utilities and production businesses report above-average exposure, while construction and transport remain close behind. Board ownership, supplier scrutiny, and formal response planning remain patchy. The companies treating cyber resilience as paperwork may satisfy part of the audit trail, but production, logistics, and recovery teams still need systems that work under pressure.